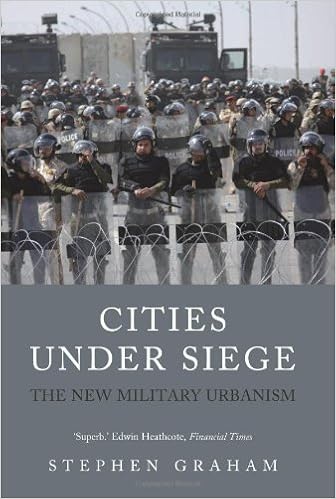
By Stephen Graham
ISBN-10: 1844673154
ISBN-13: 9781844673155
A strong exposé of ways political violence operates throughout the areas of city life.
Cities are the recent battleground of our more and more city global. From the slums of the worldwide South to the rich monetary facilities of the West, Cities lower than Siege strains the unfold of political violence in the course of the websites, areas, infrastructure and logos of the world’s swiftly increasing metropolitan components.
Drawing on a wealth of unique learn, Stephen Graham indicates how Western militaries and safety forces now understand all city terrain as a clash sector inhabited by way of lurking shadow enemies. city population became pursuits that have to be constantly tracked, scanned and regulated. Graham examines the transformation of Western armies into high-tech city counter-insurgency forces. He appears on the militarization and surveillance of overseas borders, using ‘security’ issues to suppress democratic dissent, and the enacting of laws to droop civilian legislation. In doing so, he finds how the recent army Urbanism permeates the total textile of city lifestyles, from subway and delivery networks hardwired with high-tech ‘command and control’ platforms to the insidious militarization of a favored tradition corrupted through the all-pervasive discourse of ‘terrorism.’
Read Online or Download Cities Under Siege: The New Military Urbanism PDF
Similar security books
David G. Coleman's Real-World Nuclear Deterrence: The Making of International PDF
The specter of nuclear guns didn't fade away with the cave in of the Soviet Union. particularly, the geopolitical problems of the post-Cold conflict period and the increase of world terrorism have ensured that they continue to be conspicuously current at the global level as a major overseas difficulty. With the 8 or 9 nuclear powers holding approximately 27,000 nuclear guns of their arsenals to this present day, it really is transparent that they're the following to stick for the foreseeable destiny.
Throughout East Asia, intra-regional migration is extra regularly occurring than inter-regional events, and the region’s various histories, geopolitics, fiscal improvement, ethnic groups, and ordinary environments make it a superb case research for analyzing the connection among abnormal migration and human protection.
Sara Foresti's Security and Trust Management: 11th International Workshop, PDF
This ebook constitutes the refereed complaints of the eleventh foreign Workshop on safeguard and belief administration, STM 2015, held in Vienna, Austria, in September 2015, along with the twentieth ecu Symposium examine in machine defense, ESORICS 2015. The 15 revised complete papers have been conscientiously reviewed and chosen from 38 submissions.
- Social Security as a Human Right: Drafting a General Comment on Article 9 ICESCR - Some Challenges
- The Standard of Good Practice for Information Security
- Knoppix Hacks: 100 Tips and Tricks
- Security Protocols XVIII: 18th International Workshop, Cambridge, UK, March 24-26, 2010, Revised Selected Papers
- Syngress Force 2006 Emerging Threat Analysis: From Mischief to Malicious
- Information Security and Cryptology: 7th International Conference, Inscrypt 2011, Beijing, China, November 30 – December 3, 2011. Revised Selected Papers
Extra info for Cities Under Siege: The New Military Urbanism
Example text
For a security plan to be effective, it must be developed, maintained, and actually used. This includes the organizational processes of acquisitions, divestitures, and governance committees. In addition to all the typical business and financial aspects of mergers and acquisitions, a healthy dose of security oversight and increased scrutiny is often essential to reduce the likelihood of losses during such a period of transformation. This process usually involves reviewing any nondisclosure agreements as well as any other binding contracts or agreements that will continue after employment has ceased.
This often means combining several types of sensors or systems (CCTV, heat and motion sensors, and so on) to provide a more complete picture of detected events. 39. It doesn’t use eavesdropping methods so it isn’t sniffing. Buffer overflow attacks send strings of data to a system in an attempt to cause it to fail. 40. A knowledge-based IDS uses a database of known attack methods to detect attacks. Both host-based and network-based systems can be either knowledge-based, behaviorbased, or a combination of both.
Which of the following represent natural events that can pose a threat or risk to an organization? A. Earthquake B. Flood C. Tornado D. All of the above 32. What kind of recovery facility enables an organization to resume operations as quickly as possible, if not immediately, upon failure of the primary facility? A. Hot site B. Warm site C. Cold site D. All of the above 33. What form of intellectual property is used to protect words, slogans, and logos? A. Patent B. Copyright C. Trademark D. Trade secret 34.
Cities Under Siege: The New Military Urbanism by Stephen Graham
by Steven
4.4



