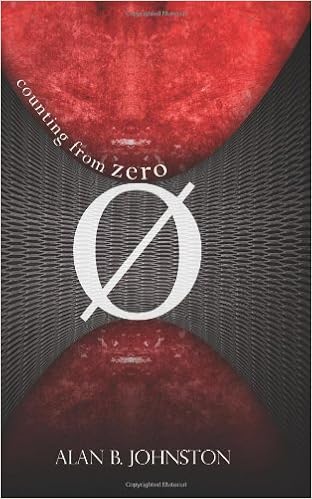
By Alan B. Johnston
ISBN-10: 1461064880
ISBN-13: 9781461064886
Can a safety professional retailer the net from a catastrophic 0 day cyber assault by way of a community of zombie pcs, often called a botnet? At what cost?
"Credible and plausible, this tale is informed by way of a subject specialist. i couldn't wait to determine what occurred next." - Vint Cerf, net pioneer
"The probability to the web from worms, viruses, botnets, and zombie desktops is actual, and becoming. Counting from 0 is a smart solution to arise to hurry at the alarming situation, and Johnston attracts you in together with his tale and plausible forged of characters."
- Phil Zimmermann, writer of beautiful reliable privateness (PGP) the main widespread e mail encryption program
Today, each laptop attached to the web is less than consistent assault from viruses, worms, port scans, and unsolicited mail. defense execs continuously struggle to comprise newly unleashed cyber assaults, referred to as 'zero day' assaults, simply to have new assaults introduced. thousands of pcs have already succumbed, and, with no their owner's wisdom, became slave pcs - remotely managed 'zombies'. lower than the keep an eye on of geared up crime and subsidized by way of overseas governments, those pcs are morphing into collections identified within the as botnets, brief for robotic networks.
Internet safety professional Mick O'Malley is the single person who acknowledges the transforming into danger of the final word 0 day assault on the web from an immense botnet, and his distinct hacker abilities and community of co-workers allow him to struggle again. extra cyber prep than cyber punk, Mick makes use of real-life instruments and strategies to encrypt all his communications, and makes use of those talents to damage the encryption utilized by the botnet. Mick makes use of encryption on a private point, too, having a number of passports and a number of names and identities. whereas crisscrossing the globe within the air, on land, and at sea investigating the risk, Mick turns into the objective of assaults on his attractiveness, his id, and eventually his life.
Along the way in which, Mick meets Kateryna Petrescu, a stunning Romanian firewall specialist. Mick's charm to Kateryna develops as they paintings heavily jointly and proportion the buzz and chance. Why is the govt. following Mick and attempting to intercept his communications? Can he cease the 0 day assault sooner than it's unleashed? what is going to be the associated fee to Mick for his unmarried mindedness?
Unfolding throughout 3 continents, the hot cybercrime secret "Counting from Zero" supplies a pragmatic insider's view of the thrust and parry international of machine safety and cryptography, and the very actual possibility of botnets.
Read or Download Counting from Zero PDF
Similar security books
The specter of nuclear guns didn't fade away with the cave in of the Soviet Union. fairly, the geopolitical issues of the post-Cold warfare period and the increase of worldwide terrorism have ensured that they continue to be conspicuously current at the international level as a major overseas hindrance. With the 8 or 9 nuclear powers preserving approximately 27,000 nuclear guns of their arsenals to at the present time, it really is transparent that they're the following to stick for the foreseeable destiny.
Throughout East Asia, intra-regional migration is extra familiar than inter-regional activities, and the region’s different histories, geopolitics, monetary improvement, ethnic groups, and typical environments make it an exceptional case learn for studying the connection among abnormal migration and human protection.
Security and Trust Management: 11th International Workshop, by Sara Foresti PDF
This e-book constitutes the refereed court cases of the eleventh foreign Workshop on protection and belief administration, STM 2015, held in Vienna, Austria, in September 2015, along side the 20 th eu Symposium study in computing device defense, ESORICS 2015. The 15 revised complete papers have been rigorously reviewed and chosen from 38 submissions.
- Der IT Security Manager: Aktuelles Praxiswissen für IT Security Manager und IT-Sicherheitsbeauftragte in Unternehmen und Behörden
- Advanced Persistent Threat: Understanding the Danger and How to Protect Your Organization
- Security and Protection in Information Processing Systems: IFIP 18th World Computer Congress TC11 19th International Information Security Conference 22–27 August 2004 Toulouse, France
- [Article] Neural Solutions for Information Security
Extra info for Counting from Zero
Example text
The avenue’s continued closure has produced unintended economic and psychological consequences, including:11 Businesses have moved out of the area—traffic volumes and congestion at key intersections as a result of the need to redirect traffic around the closure have increased overhead costs in terms of delivery and consignment charges. ”12 There is reduced productivity in businesses in the surrounding area—commute times for employees working in the area around the closure have reduced their overall productivity.
By requiring building FSD certification, the city has made involvement in evacuation planning and training at the building level both mandatory and regulated. -49- Best Practices: Chicago (continued) • Office of Emergency Communications − Office coordinates communications for fire, police, EMS − High-rise buildings must submit on CD: • Floor plans • Evacuation routes • Contact information • Locations of those requiring special assistance • Other vital data − Data can be transmitted in real-time to onscene responders High-rise buildings must now provide the Chicago Office of Emergency Communications (OEC) with a compact disc (CD) at least every six months containing detailed floor plans, evacuation routes, text documents for each floor, contact information for the entire building, a file showing occupants needing special evacuation assistance, their specific location and the type of assistance required, and a host of other vital building data, all in standard formats.
These measures have two goals: (1) keeping out of the building those people who present themselves to enter and do not belong or may inflict harm, and (2) gaining an awareness of those people, either inside or outside the building, who arouse suspicion. The threats that these measures would prevent are lower consequence threats. First, those seeking to inflict critical or catastrophic harm are unlikely to present themselves to enter. Second, those who gain access are unlikely to do so with implements or equipment capable of inflicting critical or catastrophic harm.
Counting from Zero by Alan B. Johnston
by Edward
4.2



